Security Insights
So you need a security program - Part 1
 By John Svazic
By John Svazic 
Happy New Year everyone! It’s 2020, and I felt that we should start the year (and the decade) by building a foundation for cyber security at any organization, namely a security program.
Stop me if you’ve heard this one before. Your a spry young company, having grown to a size where you’re regularly getting called in for an RFP and then one of the questions they have for you is “Please describe your security program.” You freeze, not sure what to write down. You write something along the lines of “we take the security of our customer’s data seriously” and hope that suffices. If this sounds at all familiar, then this post is for you.
This will actually be the first post in a series of posts I want to do over the coming weeks that will go through what a security program is, why every company should have one, and why they can be hard to get started if you don’t know what you need.
What is a security program?
One of the biggest questions most organizations have is what exactly is a security program? Well, a simple definition is that a security program outlines how your organization functions when it comes to protecting information through guidelines, policies, procedures, and controls. A security program isn’t a single control, policy, or procedure; it’s a collection of these that work together to make sure you “take the security of your customers seriously.” Yeah I said it. But it’s true.
What’s the core of a security program?
One of the first things we learn as cyber security professionals is the concept of the CIA Triad . No, this is not some new shadow branch of the US Government - CIA stands for Confidentiality , Integrity , and Availability .
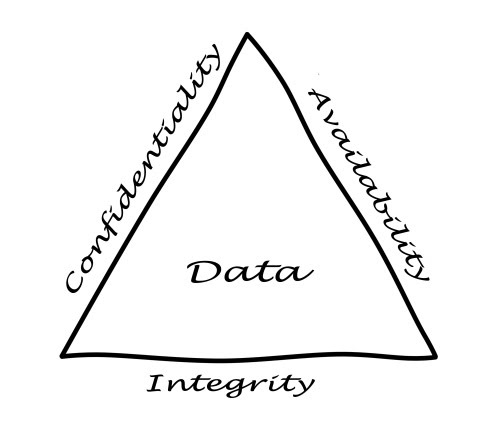
The goal of any security program is to ensure that we maintain these three aspects of the data stored within the organization. That is if we fail in any one of these, we may face an unwanted event such as a data breach, loss of trust, or lost customers.
How do I start a security program?
So you want to start a security program. Great! The good news is you don’t exactly have to start from scratch. There are a few options available to you, and throughout this series I will be going through a few of them. Specifically, I’ll be looking at:
-
NIST Special Publication 800-53
-
The CIS Top 20 Controls & Resources
-
NIST Cybersecurity Framework (CSF)
This is by no means an exhaustive list. Some people would say that ISO27001 or SOC2 would be security programs as well, but that’s not quite true. Those are certifications that do test to see if you have a security program in place (amongst other things), but they are also fairly heavy and often beyond the scope of most small-to-medium sized organizations just due to cost.
COBIT would be the only other framework I was considering to add to this list, but my familiarity with COBIT is small and I didn’t want to mislead anyone. That and it covers a lot more than just security controls.
Regardless of the type of security framework you want to use to start building your own security program, the main focus should be around the CIA triad - Confidentiality, Integrity, and Availability. Any person, system, disk, application, or network that contains data needs to be evaluated in terms of the security controls that maintain these attributes for the data. This is ultimately the heart of the security program.
Reading one of the documents above is definitely a great start, but some of these can be quite overwhelming. In the next article for this series, I will take on the behemoth that is NIST Special Publication 800-53. This huge document is about as literal as can be for building a security program, and is a requirement if you are looking for FIPS 200 certification in order to work with certain US government institutions.
– John
Looking for help with your own security program? EliteSec can help. Contact us today. We will sit down with you and discuss what makes the most sense for your organization. We offer a free 1 hour consultation to determine what’s best for you.