7 Penetration Testing Best Practices for Small Businesses
You’re a small business with limited resources. How much time do you have to devote to such a complex task?

About Us
EliteSec prides itself on our professionalism and focus on helping organizations of all sizes ensure they are protected against cyber threats. Our goal is to help educate our clients and raise the security posture of as many organizations as possible to help others. EliteSec focuses on the needs of the client, offering pragmatic advice with candid discussion. Using modern technology, techniques, and best practices to educate and elevate our clients.
our philosophyAt EliteSec, we offer white-glove, boutique solutions to each of our clients, bringing over a decade of cybersecurity experience with every engagement. We start by understanding what our clients needs are, how they work, and what they have built. Once we understand where they are coming from, then we move on to offer pragmatic advice with candid discussion. This way we can find maximum value with minimum impact to their day-to-day operations.


Penetration testing helps ensure that your product is only used in the way you intended, no matter the intent of the user.
Read More
Cybersecurity is a large and complex topic, which is why finding a trusted and knowledgeable guide is so important.
Read More
Disasters rarely make it easy for your teams to recover, so why practice by following the “happy path”?
Read More
You’re a small business with limited resources. How much time do you have to devote to such a complex task?

If a web application attack can happen to giant companies like Casio, it can surely happen to your web apps too.

Based on our experience running pen tests for our clients, the average pen test takes 2 to 4 weeks to complete.
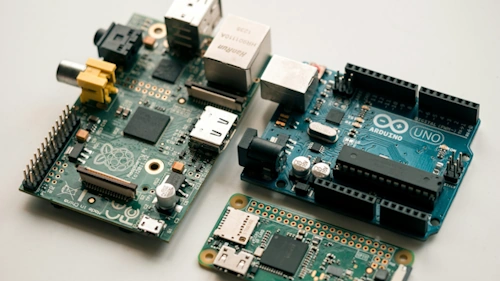
I have recently re-visited my builds of a dropbox I use for remotely testing internal networks, and I found great success in going back and rebuilding these devices from the ground up.

It’s 2024, and for some reason, many businesses still underestimate the likelihood of an attack on their web apps.

A surprise they weren’t prepared for, and in hindsight, they’ll tell you that they wish they had prepared.